Given that you have likely come across the “mainstream” media perspective on the issue, I’m going to share the articles that you likely didn’t come across in your everyday standing-in-line Internet browsing, and why I think these articles are worth mention. The first section focuses on technical articles, and the second section focuses on legal articles.
For a crash course in the All Writs Act, see my post The SDK: The All Writs Act.
Let’s Get Technical
Not a Slippery Slope, but a Jump off the Cliff [Lawfare, Nicholas Weaver]
“The San Bernardino case, however, is not a tip-toe down a slippery slope but a direct leap into a dangerous world, one which would compromise all our security under an incredibly ambitious reading of the law.”
I’m glad we got that out of the way. You know, in case it wasn’t clear as to where I stand on this issue 🙂
In Apple vs. the FBI, There Is No Technical Middle Ground [MIT Technology Review, David Talbot]
“Either you let law enforcement get into encrypted devices and run the risk of letting others find a similar way in, or you don’t.”
Andy Sellars, a lawyer specializing in technology issues at the Cyberlaw Clinic at Harvard Law School:
“While the proposal might conjure images of a clean room in Cupertino where such things could be done—and the code that makes it possible can’t get out—that’s not feasible in practice. . . How long will that room really stay clean? The privacy benefit right now comes from the fact that nobody knows how to do this. Not Apple, not the FBI, and we think not the NSA, though maybe they do. . . As soon as Apple does this, there’s no way this wouldn’t get out, be stolen, be leaked. There is no way that would stay a secret.”
Michael Hayden, former director of the National Security Agency:
“when you step back and look at the whole question of American security and safety writ large, we are a safer, more secure nation without backdoors.”
Does the FBI Really Even Need Apple’s Help? [ACLU, Daniel Kahn Gillmor & Jay Stanley]
“. . . In other words: passcode + UID = unlocking key and access to data.. . . In short, the phone’s UID is everything. With it, the FBI can get what they’re asking for. Without it, they can’t.”
Now with that in mind, the particularly helpful piece of this article is the great explanation of the phone UID:
“The fuses in Apple’s chips are just like the fuses in your home’s wiring—electrical connections designed to “blow” when too much current flows through them. Imagine 256 fuses in a row. For each fuse, flip a coin. If it comes up heads, send enough current across the fuse to make it blow. If it comes up tails, leave the fuse alone. This series of blown or not-blown fuses—in minature, inside the chip during Apple’s manufacturing process—constitutes the UID key. Apple says that no one has a record of that UID key for any phone.”
Now Come Up With Any and All Analogies For An Encrypted iPhone to Something That Existed in the 1700s. Go!
People have been applying all sorts of arguments for and against compelling Apple to decrypt the iPhone. The All Writs Act is of course at the core of the debate, but there are 2 Constitutional Amendments at the forefront of the debate.
The First Amendment
Deep Dive: Why Forcing Apple to Write and Sign Code Violates the First Amendment [EFF, Andrew Crocker and Jamie Williams]
“Apple is being forced to actually write and endorse code that it—rightly—believes is dangerous. And in doing so, it is being forced to undermine the trust it has established in its digital signature. The order is akin to the government forcing Apple to write a letter in support of backdoors and sign its forgery-resistant name at the bottom. This is a clear violation of Apple’s First Amendment rights, in addition to being a terrible outcome for all the rest of us who rely on digital signatures and trustworthy updates to keep our lives secure.”
I hadn’t even considered this perspective. The article is a great read, but I know that, because it is both highly technical and highly legal, it’s probably more complicated than most of my readers care to taken on.
The ABC’s version:
Unless your iPhone is jailbroken, you can only run Apple Apps. The thing that keeps your iPhone from being able to run any other Apps (you can’t exactly download Android Apps… like at all…) is Apple’s “digital signature”. If an App doesn’t have one, the App won’t run on an Apple device. To break it down even further, pretend “Apple” is the most popular girl in school in the following analogy:
If the most popular girl in school tells you that you can’t sit at the cool kids’ lunch table, you can’t. And “this is a free country”. So deal with it…. Well, except the FBI wants to force her to say that the FBI can sit at the table. But you can’t force anyone to say anything right? Isn’t that the whole point of the whole “right to free speech” thing?
Full disclosure: I just applied to an internship at the EFF. That doesn’t make the ideas discussed in their post any less intriguing.
The Fourth & Fifth Amendments
Apple and the FBI think iPhones are safes. A philosopher explains what they really are. [Slate, Matthew Noah Smith]
“In certain philosophers’ views, that’s the wrong way entirely of looking at this dispute. An iPhone isn’t a safe. It’s an extension of the mind.. . .
“[Apple]’s lawyers have argued on First and Fifth Amendment grounds that the state cannot compel the tech giant to weaken a device’s encryption. If that is the sole, correct framing of the issue, then society faces a simple question of how to interpret existing statutes in light of constitutional constraints.
 I absolutely agree with this notion. His final note is one I find particularly intriguing: he argues that “There is no reason to allow corporate access to our minds while vigorously denying state access.” But before that, he clarifies that his end goal isn’t that we hand over our minds to the government – it’s that the companies which currently have so much access to our minds stop being able to access that information.
I absolutely agree with this notion. His final note is one I find particularly intriguing: he argues that “There is no reason to allow corporate access to our minds while vigorously denying state access.” But before that, he clarifies that his end goal isn’t that we hand over our minds to the government – it’s that the companies which currently have so much access to our minds stop being able to access that information.
Basically, he wants a SpiderOak version of Google and Facebook.
The Second Amendment
Finally, this one doesn’t appear much in current articles, Daniel Rivero at Fusion wrote about all the way back in Fall 2014, and even XKCD was on top of it “back in the day”. And I believe it’s the most critical of all of the arguments.
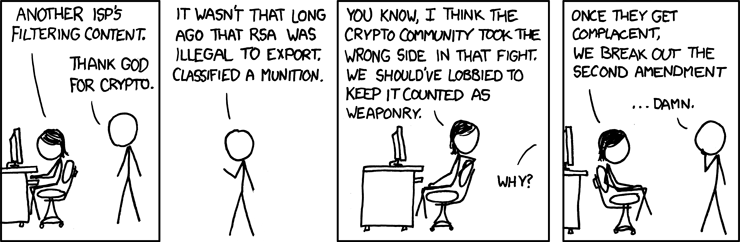
“With the new software [iOS 8], Apple claims that it would be “technically unfeasible” to comply with government warrants for data stored on iPhones, since the user alone would have the access key.. . . The situation has Internet activists bracing for a fight to protect what might be considered the second amendment of the Internet: the right to encrypt. . . That’s right, the Second Amendment. Strange as it might sound, prior to 2000, high level encryption was considered a munition that was regulated under the second amendment, which establishes the right to bear arms.. . . Some gun advocates equate the government’s presumed efforts to regulate encryption technology to an imagined government intrusion to seize firearms.. . .
Is the right to encrypt personal data and information an inalienable right that should be protected in the same constitutional breath as the right to bear arms?
We must recognize that an assault rifle— or front-loaded musket, depending on how old you are — is no longer adequate defense from the potential intrusions of government. As technology continues to change the way in which we live our lives, our rights of recourse must adapt accordingly.”
My take on the Fusion article (since I know the clip is long):
Encryption is an incredibly powerful tool. I don’t have much to add to this article besides a genuine hope that you will take a moment to consider that, in our current world, owning a gun really doesn’t do you much good. If you actually want to protect yourself (that is, if you want to protect yourself from prying eyes or any other type of unwanted intrusion, which I suppose a gun historically would have done?), then you need access to unbreakable encryption.


One thought on “The SDK: What Anyone Who’s Anyone Has To Say About the All Writs Act”